- Tue. Apr 23rd, 2024
Latest Post
Chiefs finally give Andy Reid proper care
Something wasn’t quite right in the NFL coaching landscape. Chiefs coach Andy Reid, known as one of the best in the business, was earning only $12.5 million per year, which…
Jacobs Financial Awarded Family-Owned Business of the Year
The St. Cloud Area Chamber of Commerce has recognized Jacobs Financial as the 2024 Family-Owned Business of the Year. Jim Jacobs, who was a partner in Jacobs, Willmore, and Associates,…
New $675k program offers loan assistance to small businesses in Delaware
There is a new funding opportunity available for local small and early-stage businesses that are facing challenges in securing a traditional bank loan. The Division of Small Business (DSB) in…
Testing of clay-based irrigation technology in Gozo may drastically reduce water consumption
A new irrigation method is currently being tested in Gozo by local scientists with the potential to significantly reduce water usage for plants and trees. This innovative approach involves using…
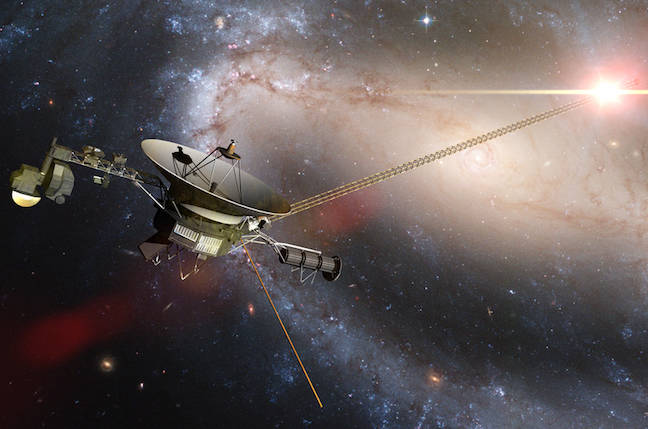
Engineers successfully patch problematic memory, restoring sanity to Voyager 1 – The Register
NASA’s Voyager 1 spacecraft has recently started sending back usable engineering data after engineers found a way to overcome a malfunctioning memory chip. The spacecraft had been producing nonsensical data…
Strengthening Community Health with Wellness and Faith
In celebration of National Minority Health Month, we are excited to share a special podcast series featuring our Strategic Alliance Partner, UPMC Health Plan. This month-long series is dedicated to…
New Panel Series Launched by Little Black Book and Comcast Technology Solutions: Reconnecting Through Engaging Content
Little Black Book (LBB) and AdFusion™ from Comcast Technology Solutions (CTS) have announced their partnership for a new season of ‘Content That Connects’. This season will feature panel discussions with…
Looking for Local Businesses to Sponsor Taste of Carbondale at SIU
The Taste of Carbondale event, set for August 14th from 1:30 to 3:30 p.m. at SIU’s Student Services Building pavilion, is a collaborative effort between Southern Illinois University Carbondale and…
Guide for AV Technology Managers on Navigating the Changing Media Landscape
The AV/IT industry is constantly evolving with new trends and best practices emerging. With the advancement of technology, there are now more cost-effective and easier-to-use solutions available for every vertical…
Headlines for Tuesday: Indianapolis News, Indiana Weather, and Indiana Traffic Updates
Jane King brings you the latest business headlines for Tuesday. One trend to consider is pursuing a trade job as they offer high pay, job security, and do not require…